For years, hiring has been treated like a throughput problem: open the req, move candidates through, close the role. But something fundamental changed. When AI can convincingly fabricate identities, employment histories, and even live interview presence, the bottleneck shifts from candidate volume to credibility.
In this environment, speed alone doesn’t create an advantage. Trust does. Most hiring teams still obsess over time-to-fill because it’s visible, measurable, and tied to revenue. But hiring is now a trust problem before it’s a staffing problem.
A 2025 survey that revealed 62% of hiring professionals said job seekers are now better at faking identities with AI than HR teams are at detecting those deceptions. That one stat should force a reset: if the candidate can convincingly simulate the signals you rely on, “speed” becomes a liability. In the same survey, 31% of managers said they interviewed a candidate later revealed to be using a fake identity, and 35% said someone other than the applicant participated in a virtual interview.
And Gartner’s trajectory line is even more sobering: by 2028, 1 in 4 candidate profiles could be fake.
So here’s the uncomfortable truth: time-to-fill optimizes hiring throughput. "Time-to-trust" optimizes hiring outcomes.
What “time-to-trust” actually measures
Time-to-trust (TTT) is the time it takes to reach a defensible hiring decision—not just a completed workflow step.
A practical definition: TTT = time from candidate entry → verified identity + verified credentials + cleared risk signals (at the level required for the role).
In other words: How fast can you know this is a real person, with real history, who matches the role’s risk profile—using evidence you can stand behind?
Because when AI can generate resumes, portfolios, references, even deepfake interviews, the question becomes:
- Did we process the candidate quickly?
- Or did we establish trust quickly?
Only one of those protects your company, your customers, and your brand.
Why screening stacks are breaking: they were built for a different era
Most screening programs still follow a legacy pattern:
- Recruiter moves the candidate forward.
- Offer goes out.
- Screening happens “downstream.”
- Issues appear late—when you’ve already invested time, access, and credibility.
That model assumes deception is rare and expensive. In 2026, deception is cheap, scalable, and increasingly automated. And the HR tech ecosystem makes it worse: point solutions everywhere, brittle integrations, inconsistent source quality, and a growing gap between “we ran the check” and “we can trust the result.”
So yes—companies are still trying to win on speed. But they’re speeding up the wrong thing. The new playbook: compress time-to-trust by moving verification upstream.
If TTT is your KPI, the strategy becomes clear: Shift verification earlier and run it in parallel. Don’t wait until “after we’re excited.” Verify before excitement becomes exposure.
The three levers that reliably compress time-to-trust
1) Identity first: “Is this a real person?” becomes the gate, not a footnote.
If identity is uncertain, everything else is noise. You don’t need “more data.” You need clean identity resolution: the ability to confirm someone’s identity by matching and validating identifiers so that downstream searches and verifications are anchored to the right individual.
In practice, identity-first means:
- Fewer false matches,
- Fewer “close enough” assumptions,
- Fewer surprises after access is granted.
- Less time wasted verifying the wrong person.
When identity is validated upfront, every subsequent check becomes faster, more accurate, and more defensible.
2) Credentials in parallel: stop letting verification sit on the critical path
Time-to-trust collapses when credential verification becomes a bottleneck. Instead of “background check, then verify,” you run credential verification in parallel — early enough that it doesn’t stall onboarding, but strict enough that it prevents bad hires from slipping through.
Most hiring programs optimize for time-to-offer, then act surprised when verification delays become the hidden drag on time-to-start. With a TTT mindset, verification isn’t paperwork. It’s risk containment. The goal isn’t just speed — it’s eliminating late-stage surprises while switching costs are still low.
3) Risk signals that keep up: one-time checks can’t be your whole truth
A single report is a snapshot. Risk is a timeline. Most screening programs are built around a single decision point. But real-world risk doesn’t behave that way.
If your trust model ends at hire, it assumes stability in a world that’s increasingly dynamic. For roles tied to compliance, safety, financial access, data security, or vulnerable populations, this gap matters. Not because something will happen — but because you won’t know if it does.
Time-to-trust isn’t just about how fast you establish confidence. It’s about how reliably you maintain it.
Continuous monitoring shifts trust from a static report to an ongoing signal — where new risk information triggers review before it becomes exposure. That’s how trust becomes operational instead of procedural.
What “time-to-trust" inside HRIS looks like
Most HRIS (Human Resources Information System) workflows were designed to move applicants through stages. The next generation will be designed to move applicants through trust thresholds.
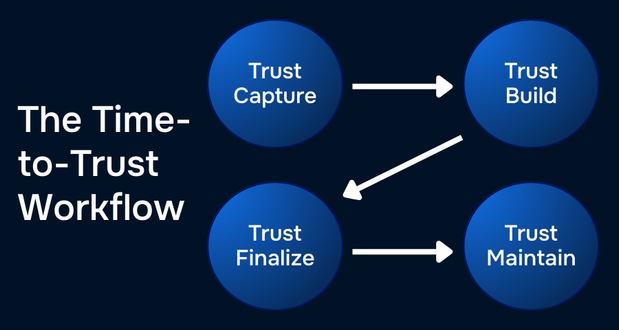
A “TTT-native” workflow looks like this: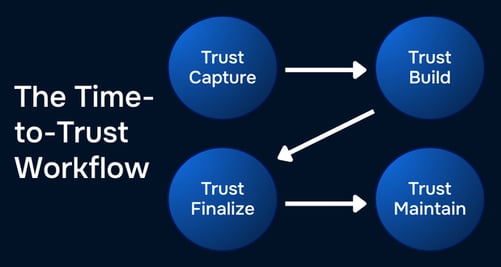
Step 1: Trust capture (at application / early screening)
- Identity confirmation + basic risk gating
- Reduce spoofed candidates before they hit recruiters
Step 2: Trust build (before offer)
- Credential verification begins in parallel
- Mismatches surface early, while switching costs are low
Step 3: Trust finalize (pre-start)
- Final screening package completes
- Decision is defensible and consistent
Step 4: Trust maintain (post-hire)
- Monitoring aligns with role risk, policy, and compliance
- Risk drift becomes an alert—not a lawsuit
This is the shift: from workflow automation to trust automation.
The hard question every HRIS and HR leader should ask right now
If two-thirds of hiring professionals think candidates are outpacing HR’s ability to detect identity fraud with AI, then the old KPI is actively misleading you.
Because you can fill roles faster and still lose:
- Money
- Customer trust
- Security posture
- Compliance confidence
- Team morale
Time-to-trust is the KPI that makes speed safe.
Want to see your time-to-trust baseline?
If your hiring funnel is optimized for throughput, it may be time to measure something more meaningful: how long it takes you to establish defensible trust.
InformData is built around verifiable people data — identity, credentials, behavioral risk signals, and continuous monitoring — designed to help organizations compress time-to-trust without increasing exposure.
For HR leaders, that means fewer late-stage surprises.
For HRIS and platform builders, that means trust embedded directly into workflow architecture.
For organizations operating in high-risk or regulated environments, that means speed that doesn’t compromise defensibility.
The next competitive advantage is simple: Make trust the system. Then make it fast.